Strengthening Cyber Resilience with Commvault

New Requirements Driving Backup System Modernization
NIST Recommendations
New regulations including NIS2, DORA
- Threat Detection
- Response and Recovery
- Backup policies and procedures, as well as methods and procedures for data restoration and recovery
Increased threats related to cyberattacks
- Readiness for restoring entire production environments – minimizing recovery times for the entire environment after a cyber (or physical) attack
National Critical Infrastructure Protection Program 2023
- Cloud evacuation plan that critical infrastructure entities must include in their protection plan
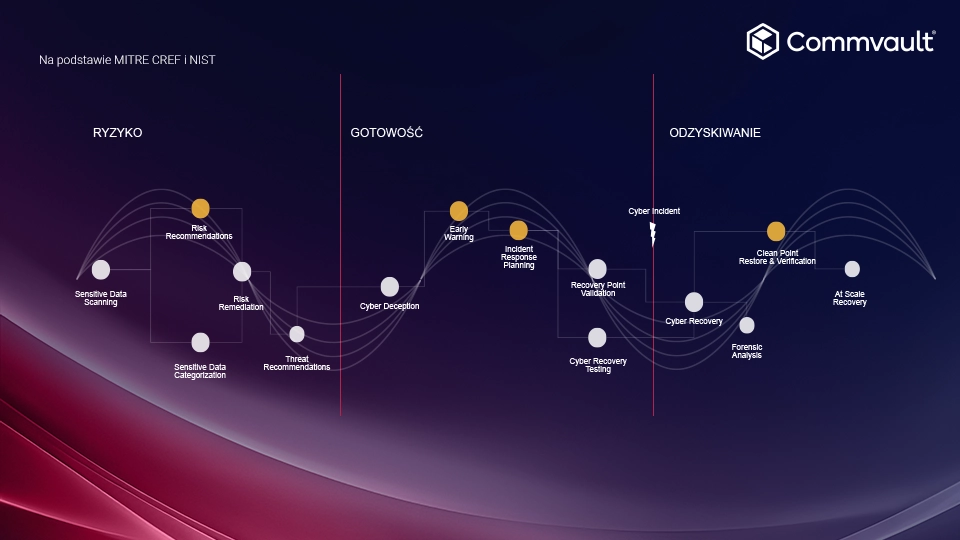
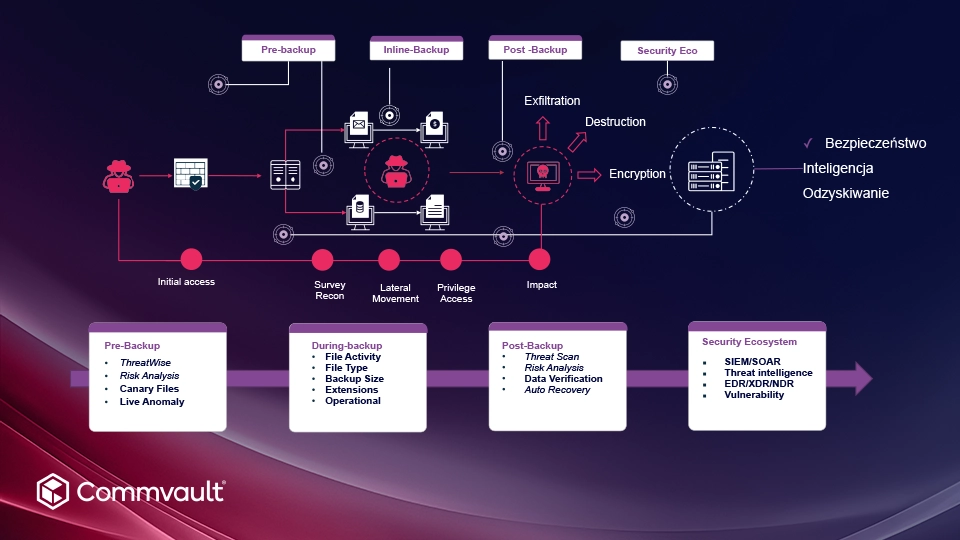
Total Resilience: True cyber resilience begins before an attack – and never ends
Commvault Zero Trust Architecture compliant with NIST
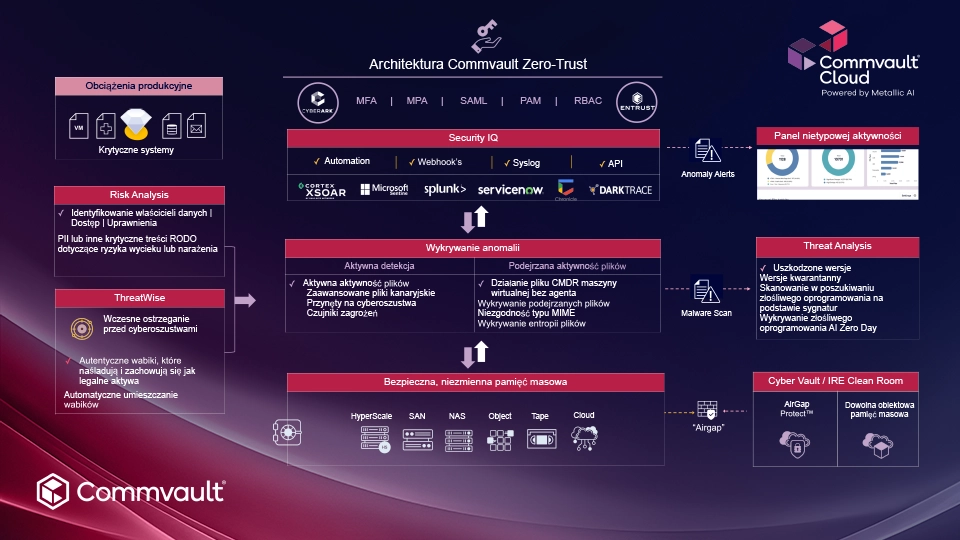
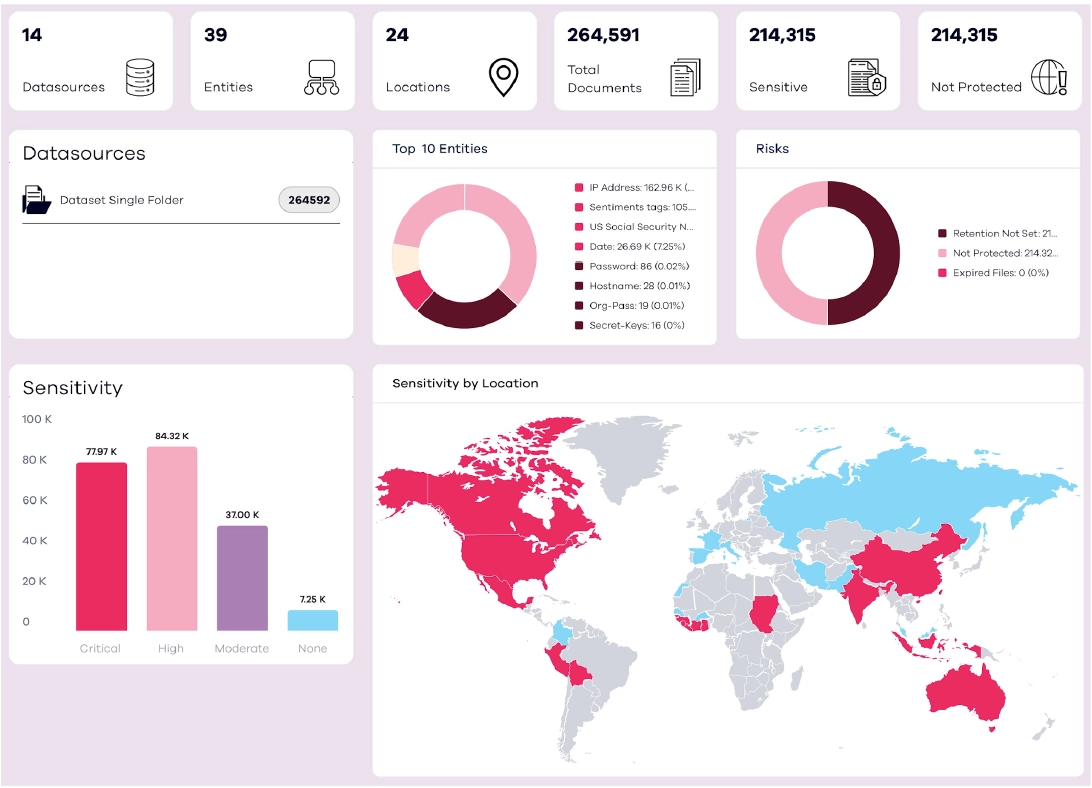
Risk Analysis: Discovering, classifying, and protecting sensitive data
- Secure and manage sensitive data to help ensure compliance.
- Rapid response to security events — before data encryption, leakage, or exfiltration.
- Identify and eliminate data ROT to reduce costs.
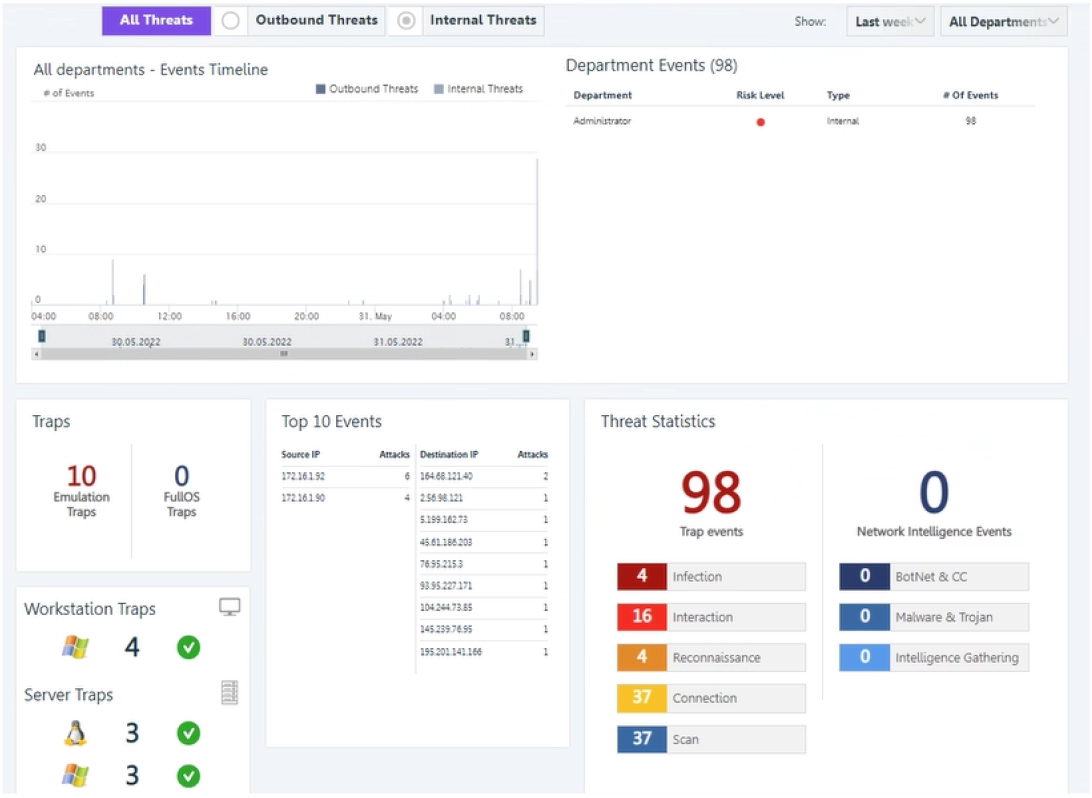
Threatwise Cyber Deception: Early warning of threats through cyber deception
- Intelligent decoys that mimic and behave like real systems.
- Precise alerts for early threat detection, without false alarms and alert fatigue.
- Robust integration with critical security tools and backup environments.
- Simple SaaS delivery with a flexible, lightweight architecture and rapid scalability.
Security IQ: Real-time threat insights and recommendations
- Assessment and continuously improved level of backup security.
- Real-time insights into critical events, unusual activity, and security vulnerabilities.
- Informed data recovery decisions to exceed SLA targets.
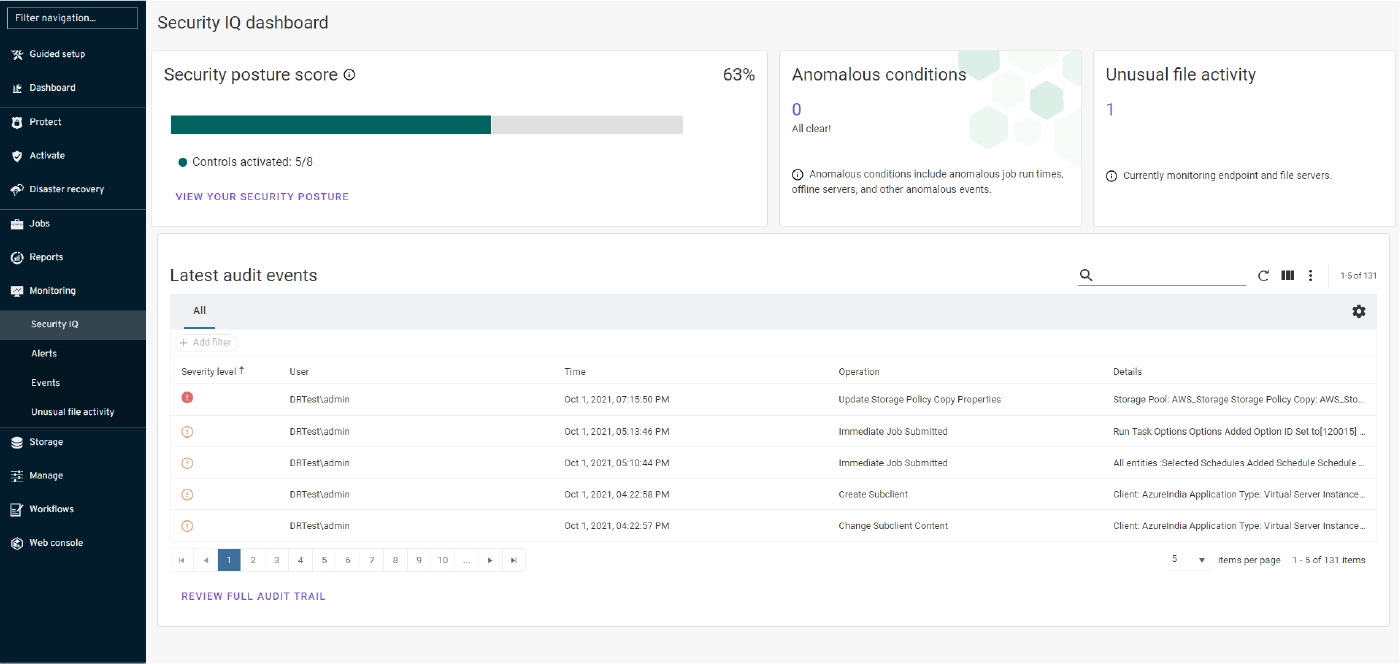
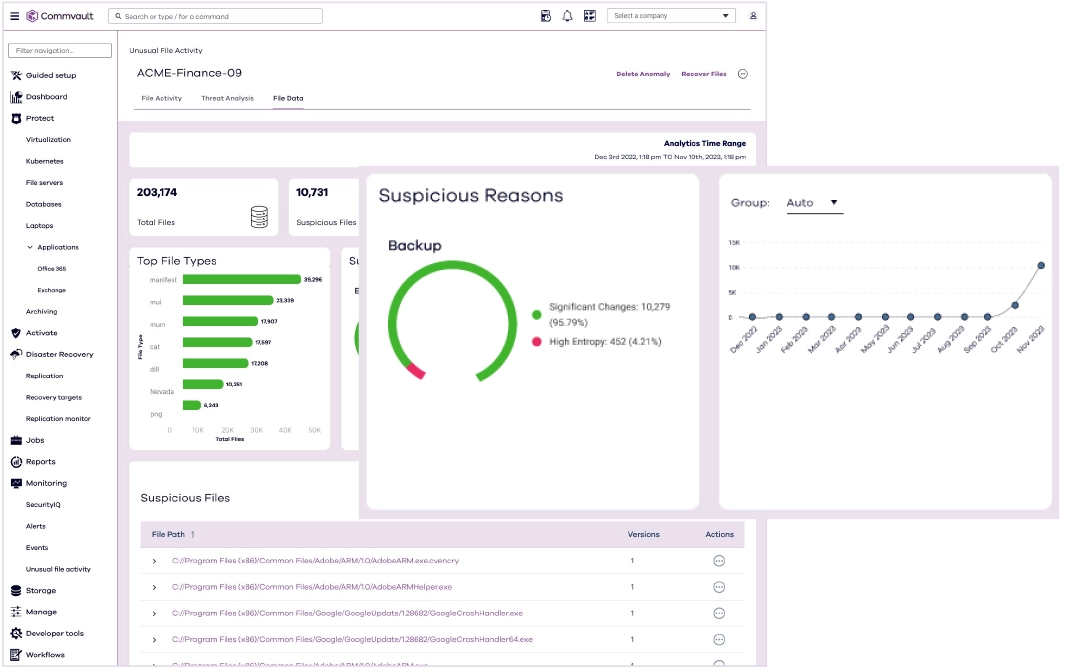
Anomaly Detection: Detecting threats and unusual activity
- Identifying threats in backups to recover only clean data.
- Detailed information that can help guide informational activities.
- Improved recovery scenarios, reducing post-recovery processes and multiple restore attempts.
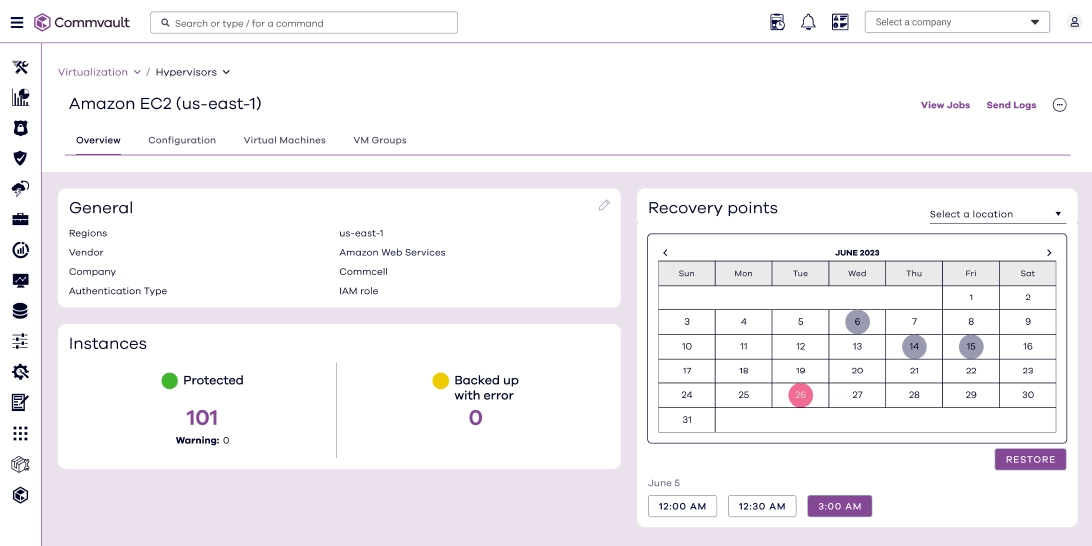
Immutable Backup Data Storage and Recovery Targets: Protecting data across all systems, no matter where it resides
- Separated control layer from the data layer and from the backup storage location.
- Rapid data recovery from anywhere to anywhere.
- Managing data of any generation to prepare for the future and unlock cloud adoption.
Anomaly Detection Layers
Contact us!
Let's talk about solutions tailored to your needs - our experts are at your disposal.
Contact Contact


