Commvault – an effective response to cyberattack threats

New Regulations including NIS2, DORA
Art. 10 DORA Detection – Commvault
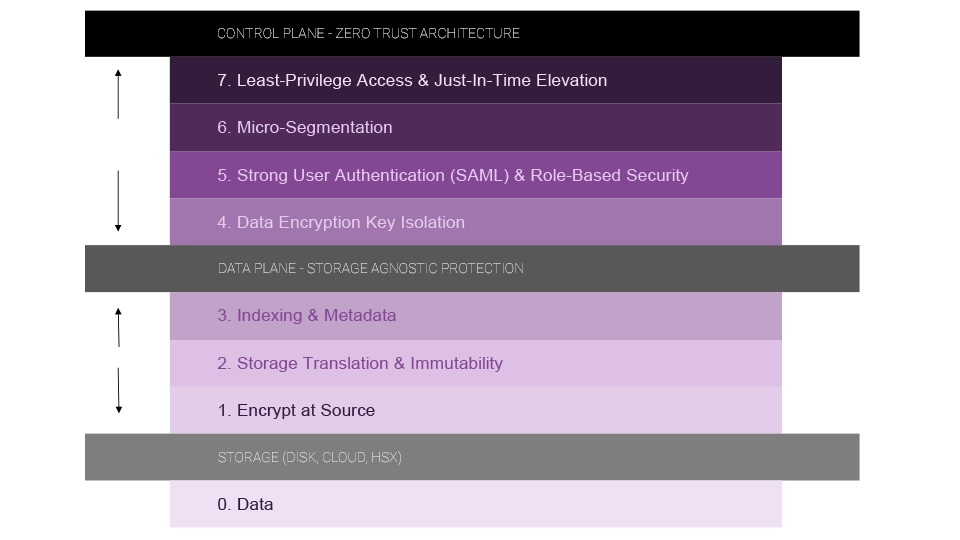
- AAA Framework
- Extended RBAC with MFA
- Ransomware detection mechanisms
- Threat analysis
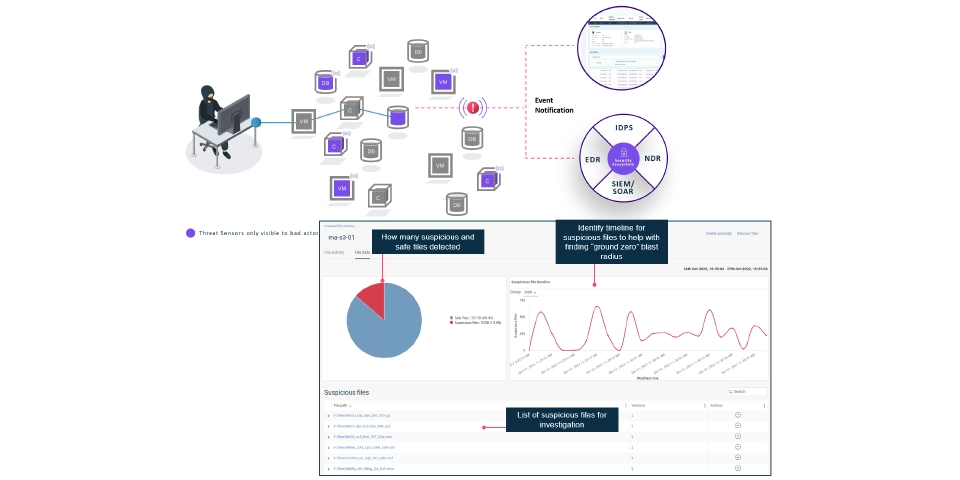
- Threatwise
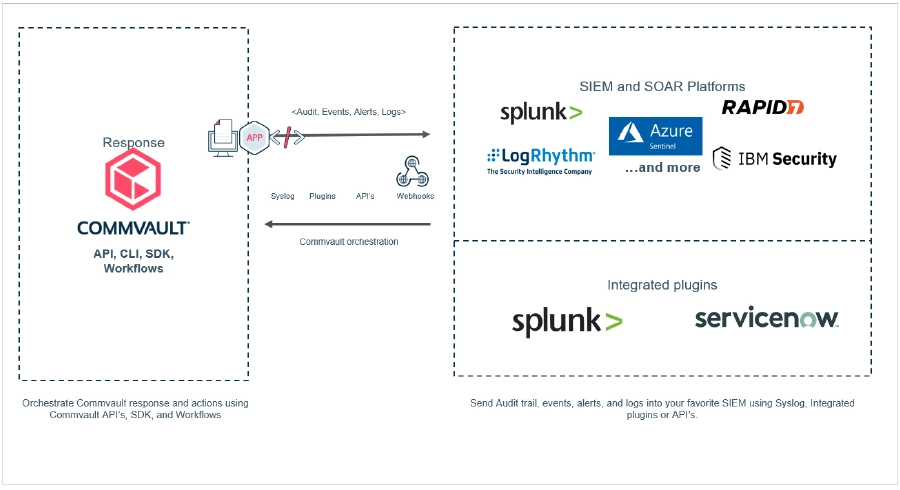
- Integration with SIEM systems
Art. 11 DORA Response and Recovery – Commvault
- AAA Framework
- Extensive reporting mechanism
- Advanced integration mechanisms with event logging systems
- Automated recovery using API and Workflow
Art. 12 DORA Backup Policies and Procedures, and Data Restoration and Recovery Methods and Procedures – Commvault
- Single point of management
- Broad spectrum of supported applications
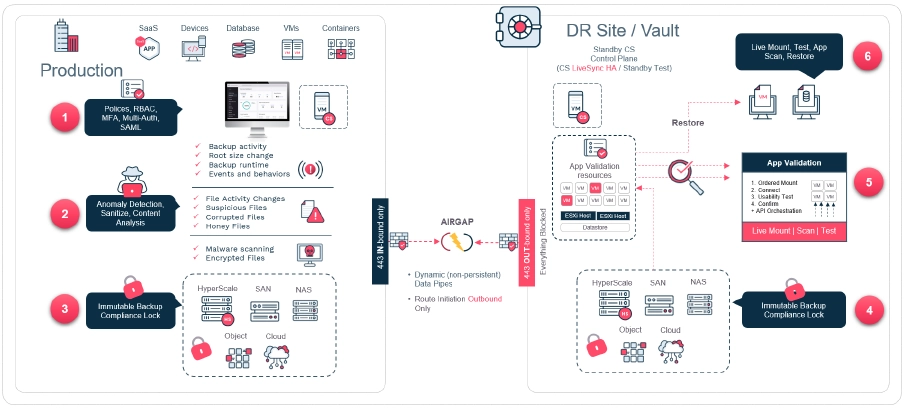
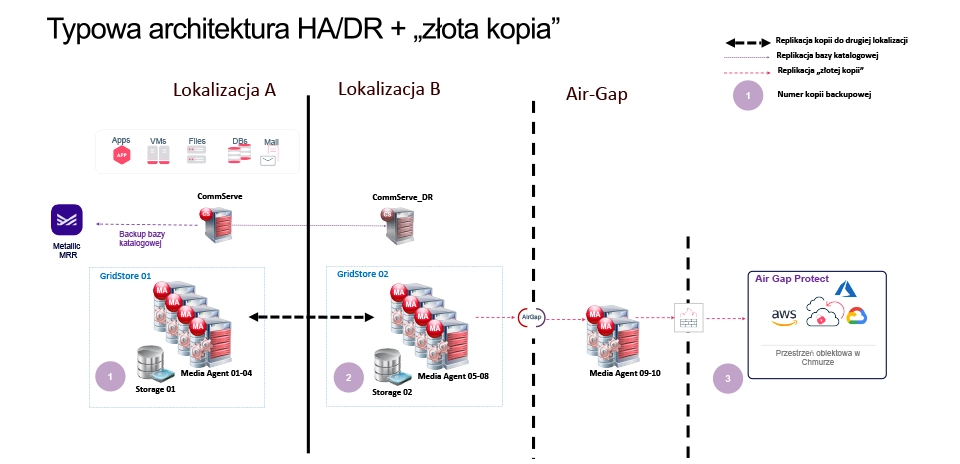
- Advanced data isolation mechanisms (Air-gap / WORM)
- Fast data recovery using snapshots and All-Flash arrays
Exit Strategy
Requirements
Ability to have an extreme exit strategy that enables the continuation of ICT services in the event of third-party disruptions. Possibility of migrating to another external ICT service provider or switching to internal solutions consistent with the complexity of the service provided.
How does Commvault support meeting the requirement?
Ability to convert between systems, cloud, and hypervisors. Enables migration of systems and data between clouds and on-premises environments. Rapid, large-scale recovery with Commvault CloudBurst.
Increased threats related to cyberattacks on critical infrastructure
Impact of all-flash arrays on backup strategies
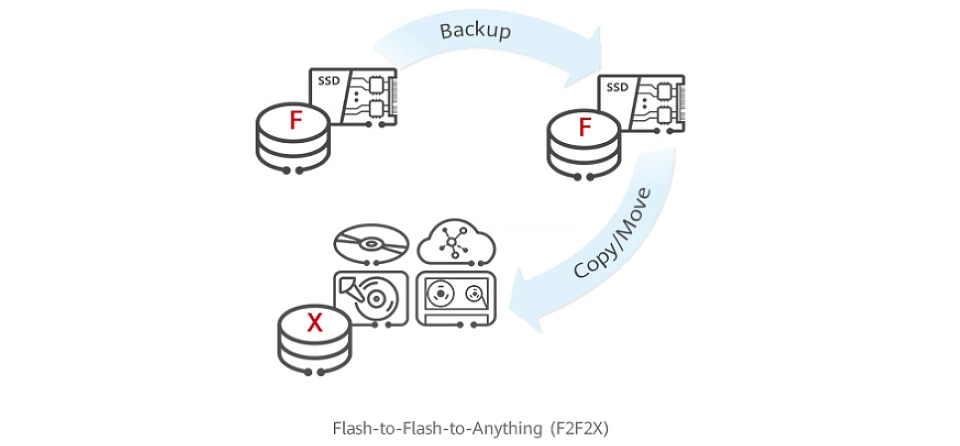
From D2D2T to F2FTX
- Traditional production arrays based on spinning disks have largely been replaced by all-flash arrays, or such replacement is planned for the future.
- The rapid growth of data volume and ransomware threats mean that the classic disk-based backup approach does not meet expected RTOs.
- Flash-to-Flash-to-Anything (F2F2X) opens up new possibilities.
New capabilities
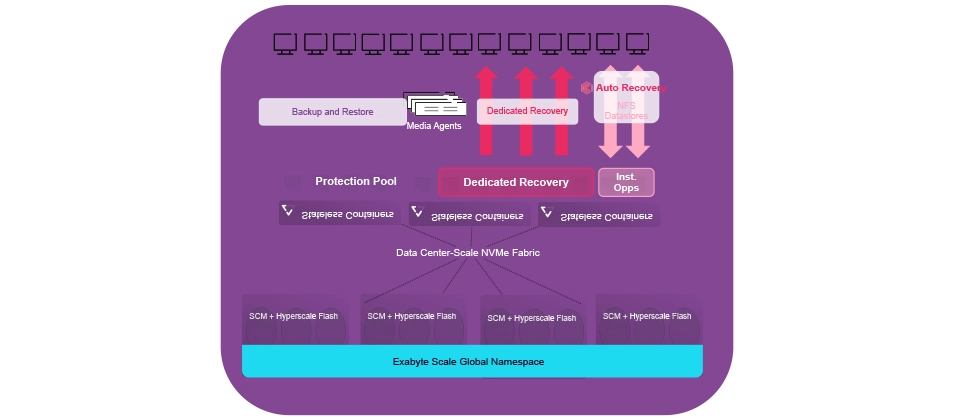
Operational continuity at flash speed
- Eliminates the need for virtual machine restoration when using Commvault Auto Recovery / Disaster Recovery.
- Ability to run machines directly from the backup array with near-production performance.
- Regular and frequent Disaster Recovery tests.
- Meeting SLA requirements and expanding functionality in DEV / TEST areas.
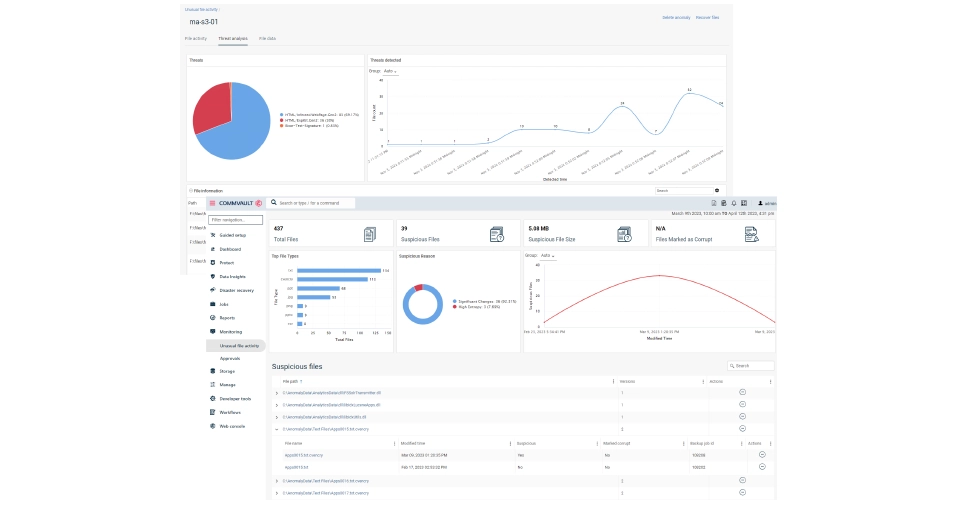
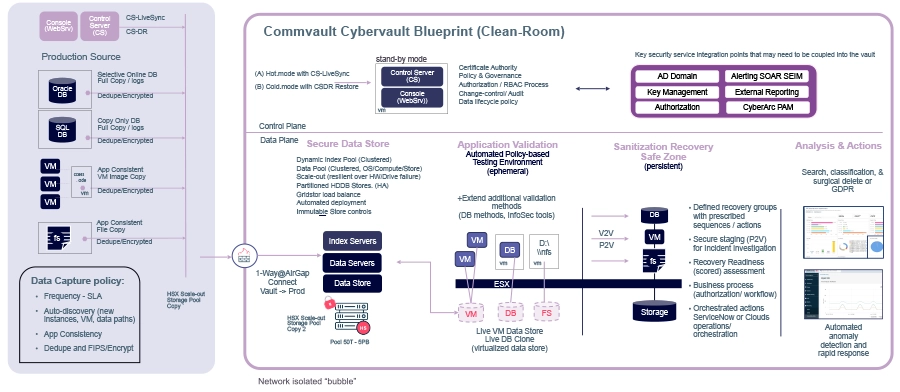
Secure recovery – Threat scan
Mallware-free backup
- Recovery after a ransomware attack requires a different approach than classic disaster recovery.
- Scanning backups for malware reduces recovery time – eliminates the need for additional scanning after restoration.
- Multiple scanning algorithms:
- File extraction – examines binary headers of file types,
- File entropy – examines entropy (changes) between file versions,
- SIM hash – compares file checksums (hashes),
- Signature based – algorithm based on Avira’s built-in scanning engine.
Secure recovery – Threat scan – flexible architecture
Secure scanning
- Files are deleted immediately after being processed by the Threat Scan scanning engine.
Isolation capability
- Threat Scan can be integrated with an isolated environment (Air-Gap Protect/Clean Room), but can also be deployed for a production environment.
- Isolation is provided by Commvault® topology and tunneling mechanisms.
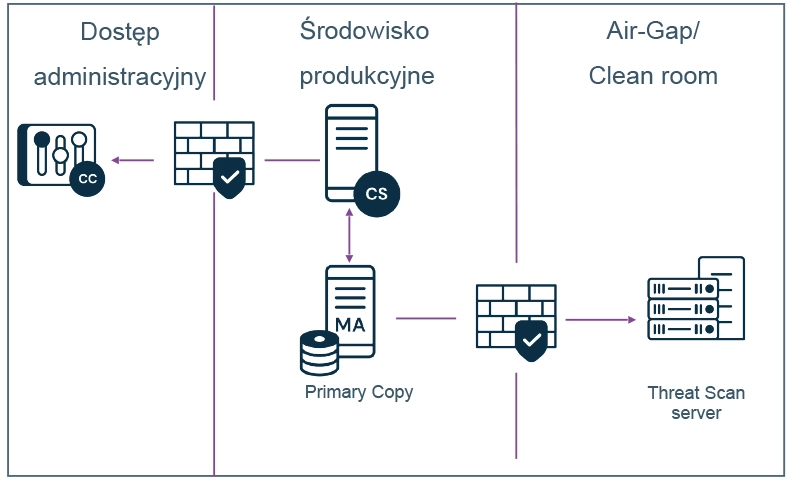
Automated recovery plan with data verification Planning a “clean” recovery site with data copies, computations, and deep content analysis
National Critical Infrastructure Protection Program 2023
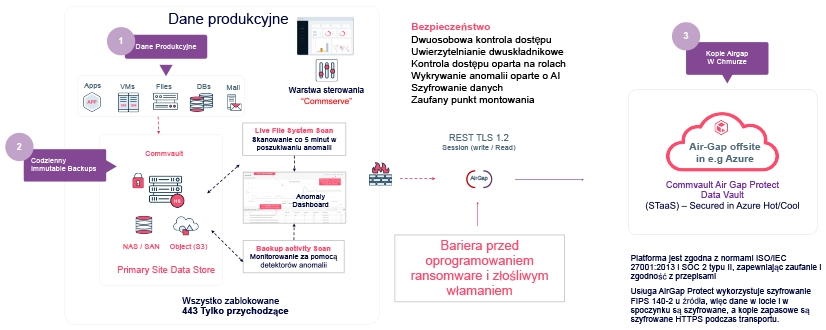
Public cloud as the last line of defense
- The war in Ukraine showed that IT resources of critical infrastructure became targets of attacks.
- Public cloud computing allows for geographical separation of critical infrastructure resources.
- Commvault’s native deduplication combined with the ability to replicate only unique blocks allows for efficient use of cloud space.
- No need to run costly appliances in the cloud for data replication.
Commvault AirGap – the last line of data protection
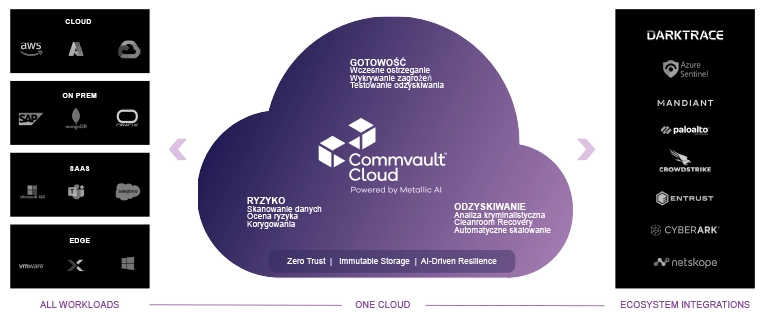
Cloud Readiness: Use Cases
Simplicity of data protection on-prem and in the cloud
- One management tool.
- Streamlined, integrated, secure migrations.
- Moving older backup data to the cloud.
Transparent reports, easy to share.
Finding and removing threats related to critical and sensitive data on-prem and in the cloud.
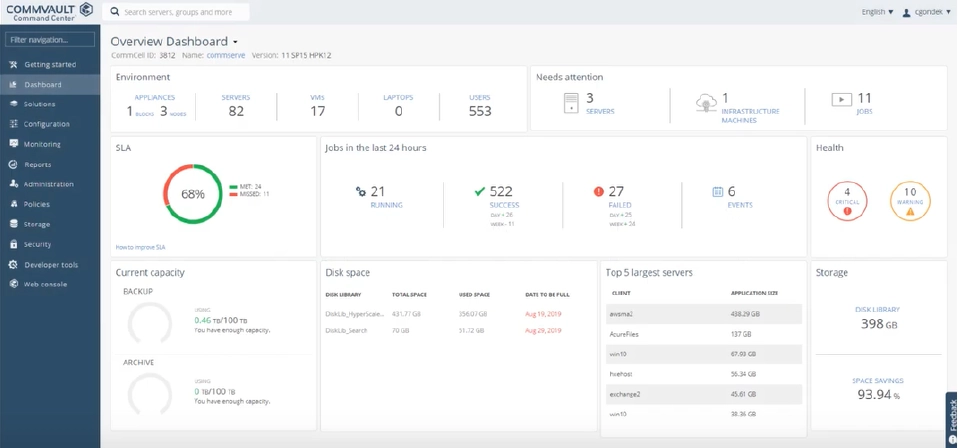
Tech demo: multi-cloud data management, migration, and recovery
Unikalna elastyczność konwersji i replikacji
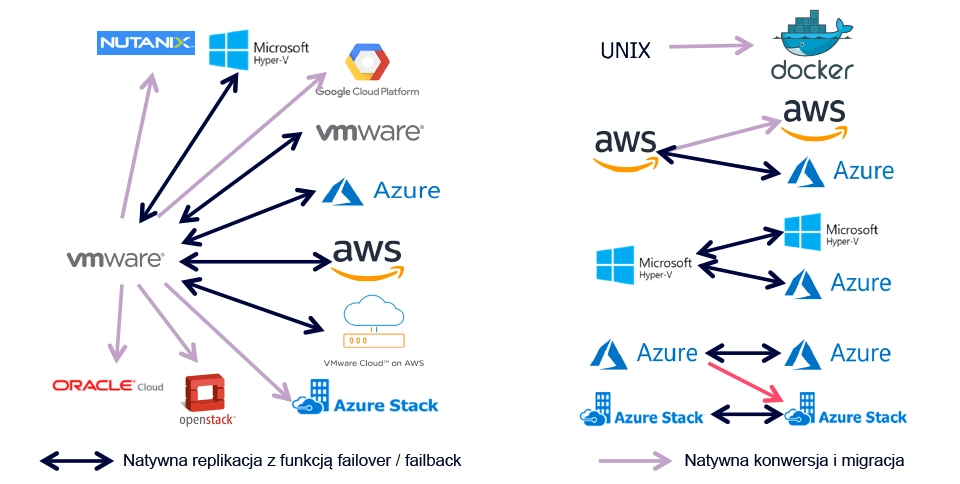
Jedna platforma. Wszystkie systemy. Jedna konsola.
Contact us!
Let's talk about solutions tailored to your needs - our experts are at your disposal.
Contact Contact


